Undersea Cables, AI Attacks and the Next-Gen Threat to Global Infrastructure Security
If you wanted to disrupt a country in 1995, you targeted borders, refineries, maybe a power plant or two.
In 2025, the list is far longer and much less visible:
Industrial control systems in power grids and water plants
Data centres and cloud interconnects
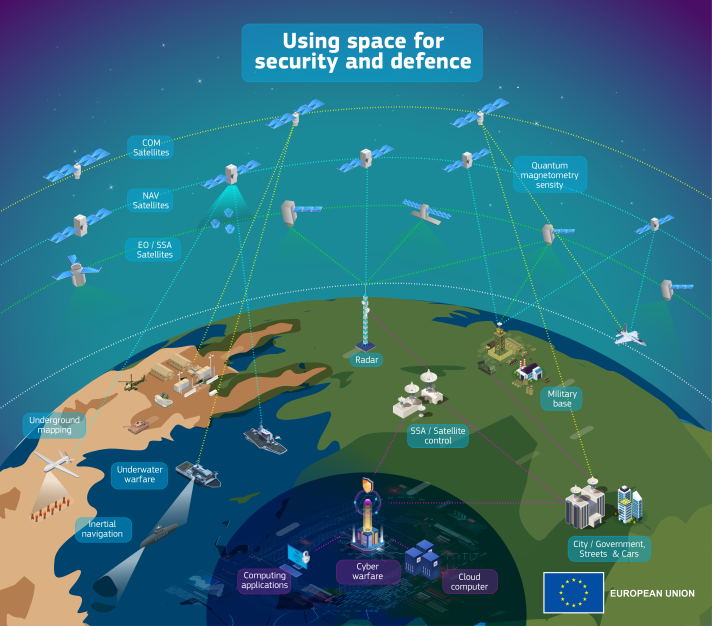
GPS and satellite links
And the undersea cables that silently carry almost all of the world’s data across the oceans
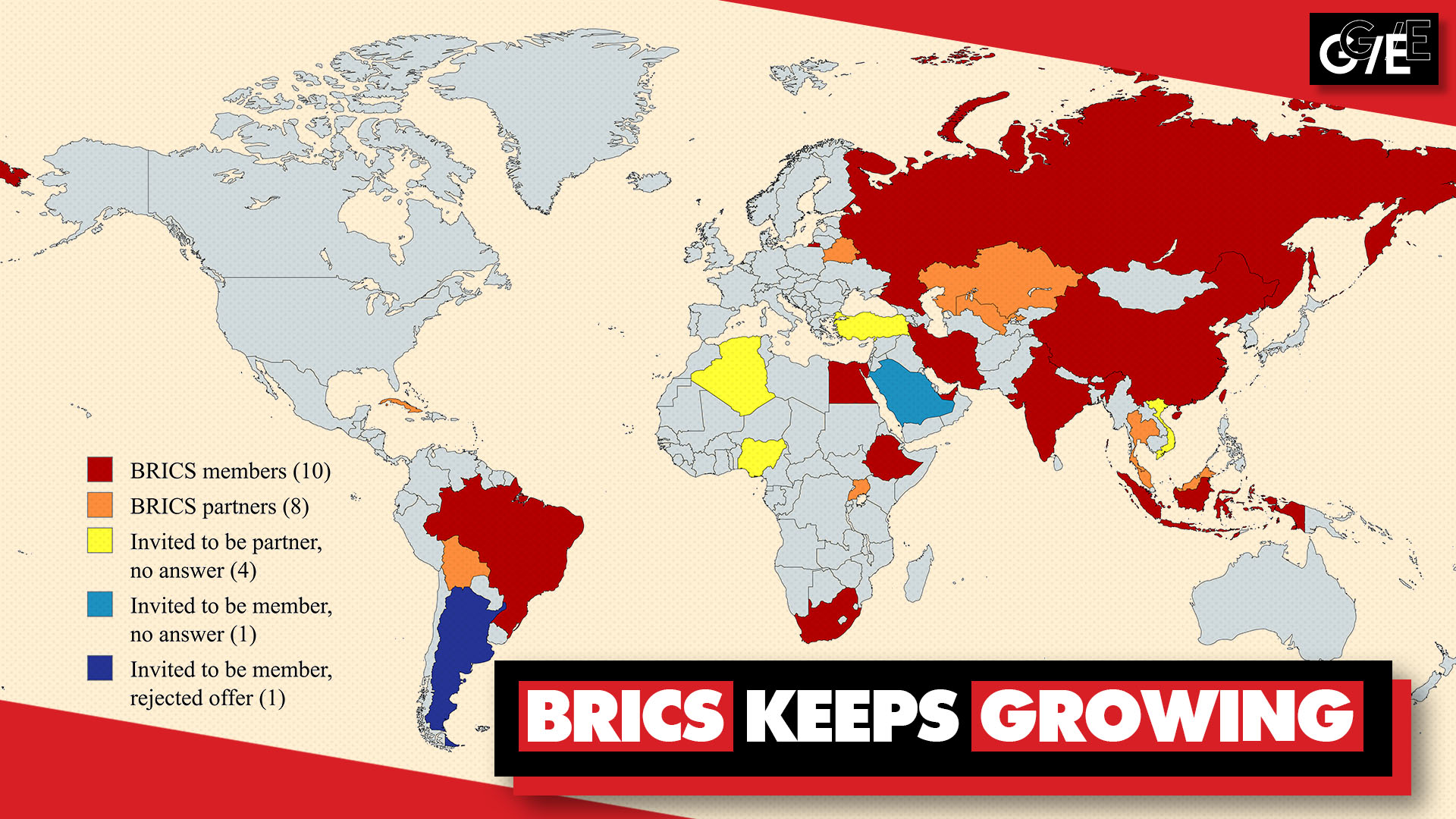
These systems, collectively labelled critical infrastructure, have become central to both national prosperity and national defence. At the same time, they are under growing pressure from AI-enhanced cyberattacks, physical sabotage, and geopolitical competition.
Global reports now consistently rank cyberattacks on critical infrastructure among the top geopolitical and business risks, highlighting growing exposure in energy, water, transport and communications.
Undersea cables are a particularly stark example. Often described as the world’s “information super-highways,” they carry over 95% of international data traffic, making them the hidden backbone of the global economy – and a tempting target.
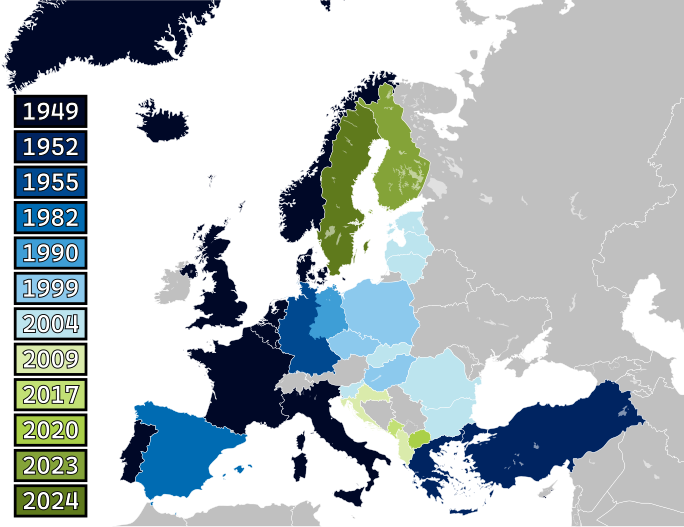
The European Union, like many of its allies, is responding. Its 2025–2030 defence and security agenda emphasises infrastructure protection, dual-use investments and readiness against large-scale attacks, including those targeting pipelines, cables and digital networks.
In this article, we’ll unpack:
What counts as critical infrastructure – and why it’s suddenly “under fire”
How AI, supply chains and undersea cables are changing the threat picture
The geopolitical fault-lines around Russia, China, the US and Europe
Policy and defence responses now emerging
Practical takeaways for governments, businesses and individuals
We’ll also connect this to themes from earlier pieces on AI in cyber warfare, cybersecurity & telecoms and Europe’s internal security stand-up, because the same technologies and networks run through all of them.
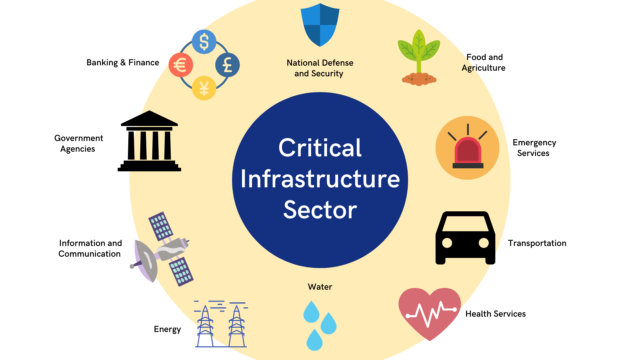
1. What counts as critical infrastructure and why it’s under fire now
Critical infrastructure typically refers to systems and assets that are essential for the functioning of society and the economy: power, water, transport, telecommunications, finance, healthcare and now, increasingly, space and data infrastructure.
Two shifts explain why this infrastructure has become a prime target:
1- Digitalisation and interdependence
Power grids, pipelines, rail networks and even water treatment plants are now deeply dependent on digital control systems and remote connectivity:
Industrial control systems (ICS) and operational technology (OT) are connected to corporate IT networks.
Remote access is common for maintenance, monitoring and optimisation.
Cloud-based services are increasingly integrated into core operations.
This connectivity boosts efficiency – but also opens doors for remote cyber intrusion. Research on ICS attacks shows how malware like Industroyer2 and operations by groups such as Russia-linked Sandworm have repeatedly disrupted Ukraine’s power grid, sometimes timed with physical missile strikes.
2- Geopolitics and hybrid warfare
States and advanced threat actors increasingly see cyber and infrastructure attacks as tools of coercion and signalling, sitting below the threshold of open war:
Cyber operations can cripple services, sow panic and force political concessions without crossing into traditional armed conflict.
Attacks on energy, pipelines or cables can signal capability, exact economic cost, or complicate military support to allies – as seen around the Russia–Ukraine conflict and incidents in the Baltic Sea.
Infrastructure is no longer a passive backdrop – it’s now primary terrain in hybrid warfare.
This is exactly the evolution we described in The Rise of AI in Cyber Warfare and in our analysis of Australia’s state-sponsor terror law: once “civilian” systems are now deeply entangled with strategic conflict.
2. The technological dimension: AI, supply chains and the ocean floor
AI-powered attacks on cyber-physical systems
AI is transforming both offence and defence.
On the offensive side, reports and research highlight that AI tools help attackers to:
Automate reconnaissance of networks and find vulnerabilities at scale
Generate more convincing phishing lures and deepfake voices for social engineering
Optimise malware behaviour to evade detection systems
On critical infrastructure specifically:
Study after study has documented the impact of cyberattacks on power grids and energy systems – from Ukraine’s repeated blackouts to attacks on oil and gas facilities.
As AI is integrated into control systems (for grid balancing, predictive maintenance, etc.), it creates new attack surfaces if models and data pipelines are not secured.
On the defensive side, AI is used to:
Spot anomalies in ICS/OT traffic
Correlate signals across IT, OT, telecom and cloud environments
Detect suspicious patterns in user behaviour or external traffic
But this is an arms race: the same machine-learning concepts used for defence can be repurposed to build smarter, stealthier attacks.
We explored this dynamic in detail in Navigating the New Threat Landscape: Cybersecurity, Telecoms & the Digital Frontier – where telecom signalling, SMS fraud and AI-enhanced scams already blur into national security concerns.
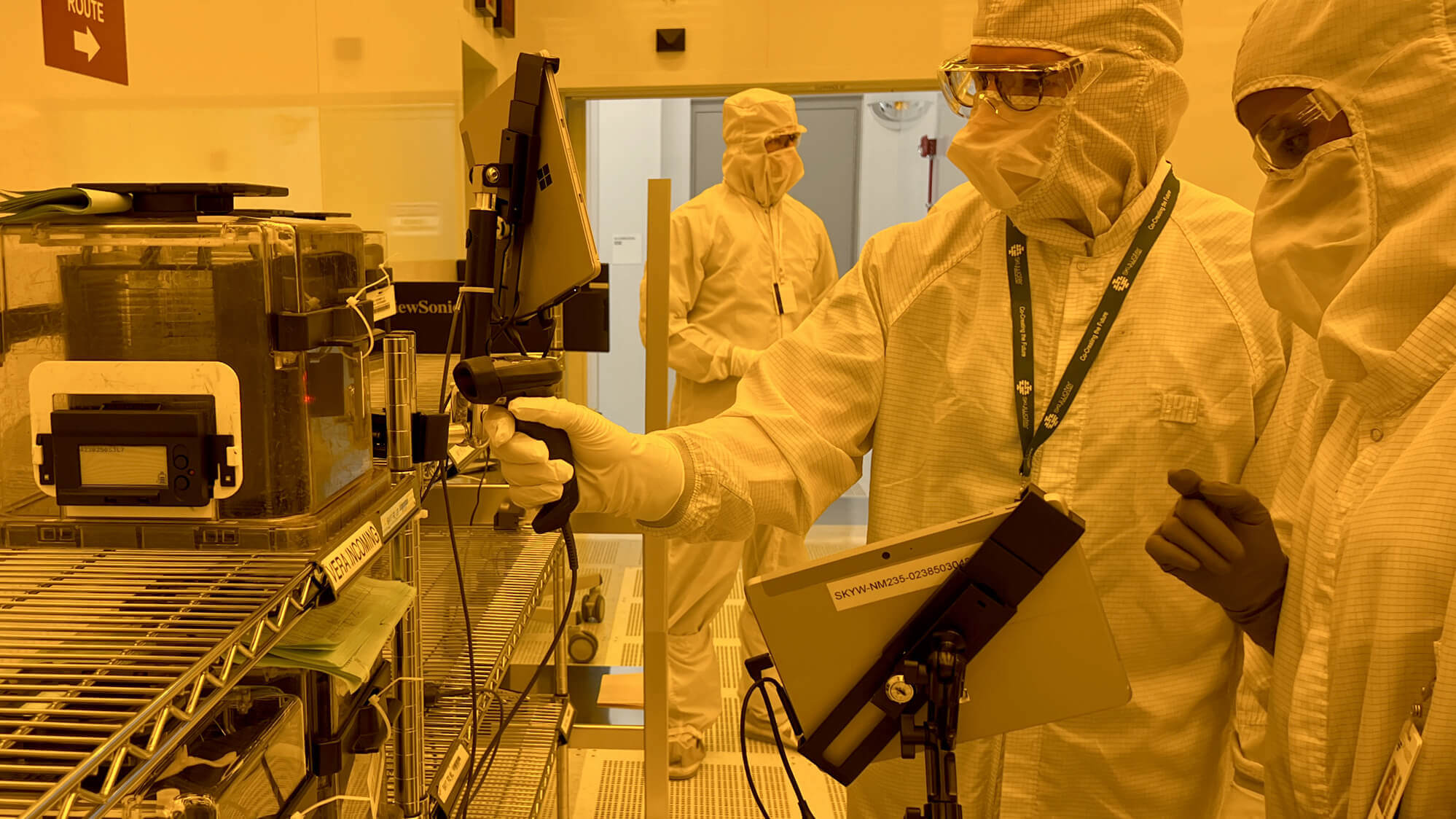
Supply-chain vulnerabilities
Modern infrastructure stacks are deep supply chains:
Hardware from multiple vendors
Software components and open-source libraries
Cloud services, integrators, managed service providers
Telecom and satellite links
The WEF Global Cybersecurity Outlook 2025 and other analyses emphasise how nested dependencies make it hard to know which suppliers sit in the path of critical systems.
That has direct security implications:
A single compromised vendor or remote management tool can become a super-spreader of malware (as seen in previous supply-chain attacks like SolarWinds).
In a crisis, sanctions or export controls can suddenly cut access to key components or services.
This is why the EU’s new defence and resilience plans explicitly talk about dual-use infrastructure, critical raw materials and repair kits for underwater cables and energy systems.
Undersea cables: the invisible backbone
Perhaps the starkest example of dependency is on submarine fibre-optic cables:
Over 95% of international data and voice traffic travels through undersea cables, not satellites.
These cables connect data centres, stock exchanges, governments and militaries across continents.
They are mostly owned and operated by private consortia, often involving big tech firms and telecoms.
Recent years have brought a flurry of incidents:
The Nord Stream gas pipeline explosions and subsequent damage to Baltic gas pipelines and cables in 2022–24 highlighted how seabed infrastructure can be attacked or sabotaged.
The Balticconnector gas pipeline between Finland and Estonia and several telecom cables (including the C-Lion1 link to Germany) suffered repeated damage, prompting investigations into deliberate interference.
In one case, the tanker Eagle S dragged its anchor for nearly 100km, severing multiple cables and a power interconnector – raising questions about legal accountability and the difficulty of prosecuting undersea infrastructure damage.
Analysts describe undersea cables as a “grey zone” target: vital but hard to monitor, operate in international waters, and subject to overlapping legal regimes with enforcement gaps.
As we argued in NATO’s Expansion and Arctic Militarization, the seabed is becoming a key strategic environment – from Arctic routes to Baltic infrastructure. Cables are central to that story.
3. The geopolitical dimension: infrastructure on the fault-lines
Critical infrastructure is no longer just a technical asset; it’s a geopolitical pressure point.
Russia–Ukraine: cyber and kinetic in tandem
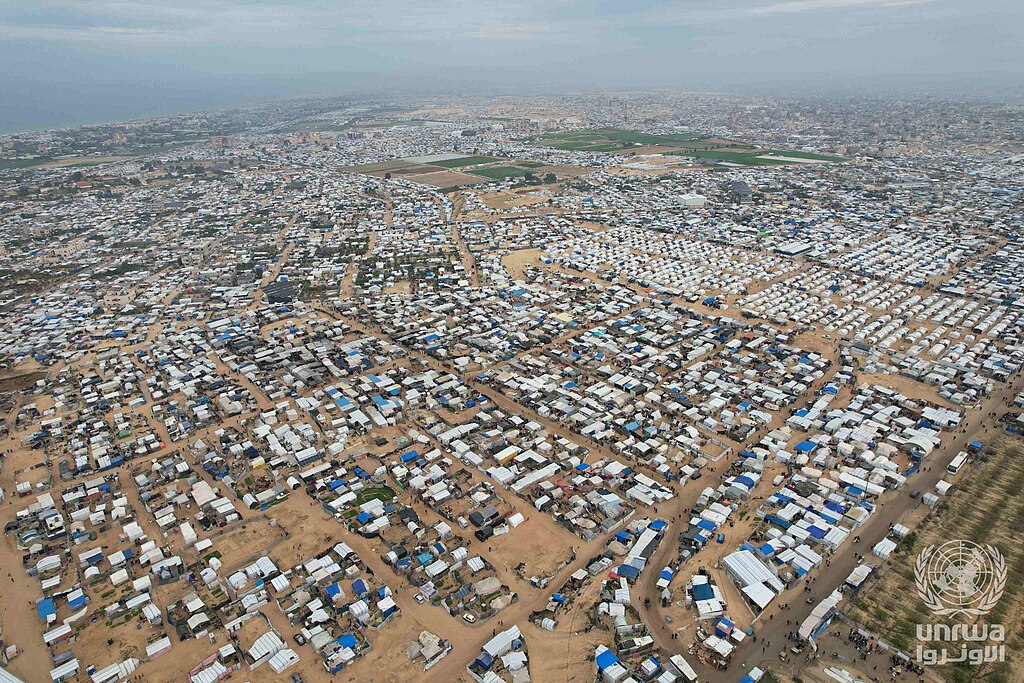
Since Russia’s full-scale invasion of Ukraine in 2022, the country has served as a laboratory for cyber–physical conflict:
Russia-linked Sandworm hackers have repeatedly disrupted Ukrainian power grids with ICS-focused malware, including during missile strikes to maximise disruption.
Ukrainian and European sources reported a 70% surge in cyberattacks on Ukraine in 2024, with thousands of incidents targeting energy, government and communications.
These attacks serve multiple aims:
Sapping civilian morale
Complicating military logistics and air defence
Testing tools that could, in theory, be reused against other countries
They also reinforce a core message: infrastructure is now both battlefield and bargaining chip.
Baltic and North Atlantic: cables and pipelines in the crosshairs
The Baltic Sea has become a hotspot of suspected infrastructure interference:
Nord Stream pipeline explosions in 2022
Damage to the Balticconnector pipeline and several telecom cables in 2023–24
New incidents in 2024–25 involving Finnish and Estonian-linked infrastructure (C-Lion1, other links)
Mapping of these incidents by think tanks such as the Wilson Center points to a pattern of pressure in northern Europe’s undersea environment, raising questions about attribution, deterrence and response.
US–China and global cable competition
Beyond Europe, US–China competition is increasingly playing out in standards, vendors and routes for undersea and 5G/6G infrastructure:
The US has pushed back on Chinese participation in certain cable projects and telecom gear, citing security concerns.
China has expanded its own digital Silk Road, including cable routes and data centre footprints in the Indo-Pacific.
The result is a world where infrastructure layout itself becomes strategic: who controls which routes, hubs and repair capabilities matters just as much as who controls territory.
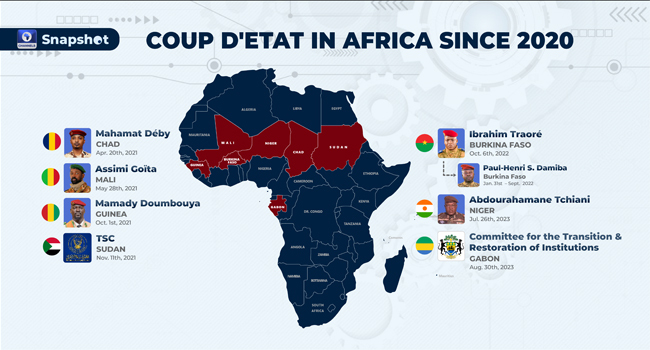
We see similar patterns in areas we discussed in African Coups and the Global Response and transnational crime & Europe’s internal security: infrastructure – whether ports, pipelines or data links – is both an economic asset and a lever of influence.
4. Policy and defence response: how states are adapting
Recognising these risks, states and blocs like the EU are rolling out policy and defence frameworks that treat infrastructure protection as a strategic priority.
EU: from NIS2 to Defence Readiness 2030
In Europe, several strands are converging:
The NIS2 Directive (in force since 2023) expands cybersecurity obligations for operators of essential services in sectors such as energy, transport, health, digital infrastructure and public administration.
In June 2025, the EU adopted an updated Cybersecurity Crisis Management Blueprint, aligning how member states and EU bodies manage large-scale cyber incidents under ENISA and the CSIRTs network.
The Defence Readiness Roadmap 2030 explicitly highlights infrastructure resilience (including space and dual-use assets) as a pillar of defence, tying cyber, physical and military mobility issues together.
Proposals to let member states tap central EU funds for defence and dual-use infrastructure, such as reinforced bridges, rail lines and pipelines that can support both tanks and trade.
On undersea infrastructure specifically:
Draft Commission documents discuss stockpiles of critical materials and repair kits for underwater cables and pipelines, and deeper cooperation with NATO and allies on seabed security.
All of this echoes our analysis in The EU’s New Centre for Democratic Resilience: Brussels increasingly treats resilience – whether of information space or infrastructure as a core security mission.
National readiness and cross-domain thinking
Outside the EU, similar patterns appear:
Governments are updating critical infrastructure protection strategies to cover cyber, physical and space assets together, rather than in separate silos.
Defence planners are integrating cyber and infrastructure considerations into operational planning, including wargaming scenarios where power or communications are degraded.
This mirrors broader shifts we’ve covered in NATO’s Expansion and Arctic Militarization and How Elections Influence Security Strategies: security policy is now inherently multi-domain.
Public–private coordination
Because much critical infrastructure is privately owned or operated, public–private cooperation is non-negotiable:
Many countries have set up sector-specific ISACs (Information Sharing and Analysis Centers) to enable timely sharing of threat intelligence across energy, finance, telecoms and transport.
Cybersecurity agencies coordinate with operators during incidents, applying the EU’s Crisis Blueprint or national equivalents to manage response and communication.
As we argued in Navigating the New Threat Landscape, telecom regulators too are joining this ecosystem, targeting misuse of signalling, SMS-based attacks and AI-enhanced fraud that intersect with national security.
5. Practical takeaways: resilience and risk management
So what does all this mean in practice for governments, businesses and individuals?
For governments and public agencies
1. Map and prioritise truly critical nodes
Identify which assets – substations, interconnectors, cables, data centres would cause systemic disruption if hit.
Treat undersea cables, landing stations and cross-border pipelines as strategic assets, not purely commercial.
2. Integrate cyber and physical planning
Run joint exercises that simulate cyber-physical incidents: e.g. a cyberattack on the grid coinciding with a cable cut or a disinformation campaign.
Ensure crisis-management frameworks allow coordination across cyber agencies, defence, energy, telecoms and foreign affairs.
3. Harden supply chains and dependencies
Use procurement rules and audits to require security-by-design from vendors.
Diversify suppliers for critical components and services; avoid single points of failure in software and infrastructure.
4. Clarify deterrence and response policies
Develop and communicate red lines and likely response options for attacks on critical infrastructure, including undersea cables – even when attribution is complex.
For businesses and operators of critical services
1. Know your dependencies
Build a detailed asset and dependency map: what services rely on which clouds, cables, data centres, vendors.
Factor in geographical risk: proximity to contested regions, chokepoints, or known hotspots for sabotage.
2. Elevate ICS/OT security
Segregate OT networks from IT where possible; strictly control remote access.
Patch ICS software carefully but regularly; monitor for anomalies using both signature- and behaviour-based tools.
3. Test failover and continuity
Ensure you can fail over between network routes, data centres or cloud regions if a cable or facility is lost.
For truly critical services, simulate operating in “degraded mode” (reduced bandwidth, intermittent power, partial system availability).
4. Plan for AI-enhanced threats
Update security awareness training to cover deepfakes, voice scams and AI-generated phishing.
Consider how attackers might use AI against your organisation – and how you can use it defensively (e.g. anomaly detection, fraud detection).
5. Engage in information-sharing
Join relevant ISACs or sector groups.
Share anonymised incident data where possible; you benefit from the same transparency when others are hit first.
For individuals and communities
Ordinary people can’t patch undersea cables – but they do play a role in overall resilience.
1. Strengthen personal cyber hygiene
Keep devices updated (especially OS and security patches).
Use strong, unique passwords with a password manager; enable multi-factor authentication (preferably app or hardware key, not SMS).
2. Prepare for service disruption
Have offline backups of crucial documents.
Know alternative ways to access savings, communicate with family or get news if primary services go down.
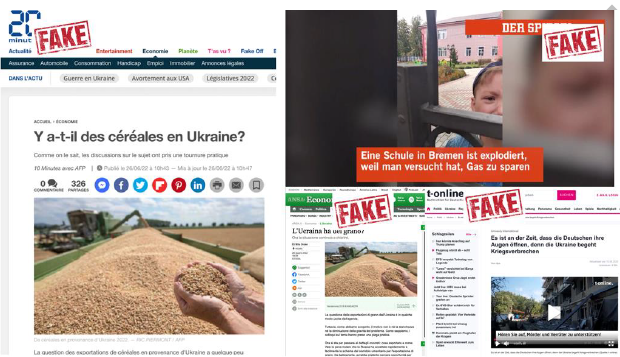
3. Be wary of crisis-driven disinformation
Infrastructure incidents often come with information operations, including rumours and fake narratives.
Follow trusted, verified sources for updates – a key theme we explored in Europe’s disinformation defence.
Infrastructure as the new front line
From AI-enhanced malware in power grids to mysterious damage on the seabed, critical infrastructure is now at the heart of global security and geopolitics.
Cyberattacks on energy, water and communications systems have surged and are increasingly tied to state-backed campaigns and hybrid warfare.
Undersea cables, carrying over 95% of international data, have emerged as strategic targets and vulnerabilities, especially in contested regions like the Baltic Sea.
The EU and allied democracies are racing to update defence roadmaps, cyber crisis blueprints and infrastructure policies to keep pace.
In earlier pieces – on AI in cyber warfare, NATO’s changing posture, transnational crime and cyber & telecom security – we’ve argued that modern security is defined by networks, flows and data, not just borders.
The emerging focus on critical infrastructure is the clearest expression of that reality yet.
For governments, the challenge is to anticipate and harden – before a crisis creates the political will. For businesses, it’s to treat infrastructure risk as a board-level issue, not just an IT problem. And for individuals, it’s to recognise that our everyday digital habits and resilience plans are now part of a much larger security picture.
The cables on the seabed, the switches in substations, the bits flowing through fibre: they may be invisible, but in the next decade, they will be as strategically important as any tank, missile or fighter jet.