Securing the Unseen How Telecoms, Devices and Cyber Threats Shape National Defence
Ask most people what “national security” looks like and they’ll picture jets, ships or troops – not a telecom switch, a software patch or a spam text.
But November 2025 has been a reminder that the real front line is increasingly invisible: buried in mobile signalling networks, tucked inside operating system updates and hidden in the data that flows between apps, devices and clouds.
In the space of a few weeks:
Telecom regulators from the UK, US, Canada, Australia and New Zealand issued a joint statement pledging tighter cooperation on network reliability, integrity and security, explicitly calling out the misuse of signalling resources like Global Titles, and threats such as SMS blasters and AI-driven fraud.
Google published the Android Security Bulletin – November 2025, including critical vulnerabilities in the System component; national cyber centres such as Canada’s Cyber Centre released advisory AV25-723, urging users and organisations to patch.
Security experts warned that the post–Windows 10 end-of-support era, after October’s final Patch Tuesday, means fewer supported operating systems – and a need for more deliberate, aggressive patch strategies as legacy systems drop off mainstream support.
For governments, this is about national resilience. For businesses, it’s about operational risk and compliance. For individuals, it’s about whether your phone, your messages and your identity remain under your control.
In this piece, we’ll unpack:
Why telecoms and devices are now central to national security
What closer regulatory cooperation means for operators and vendors
How November’s Android bulletin affects everyday users and IT teams
Practical best practices for patching, detection and supply-chain security
What to watch as AI, 5G/6G and new tech reshape the threat landscape
We’ll also connect these developments to themes we’ve explored in earlier pieces, from AI in cyber warfare to election security and disinformation – because the same forces are now shaping both digital life and hard security.
1. Why the digital frontier is now a national security issue
Over the last decade, national security strategies from Washington to London to Canberra have quietly added new pillars alongside tanks and treaties:
Cyber operations – from ransomware to state-backed hacking
Telecoms and digital infrastructure – mobile networks, subsea cables, 5G cores
Data and AI – who controls and can weaponise information
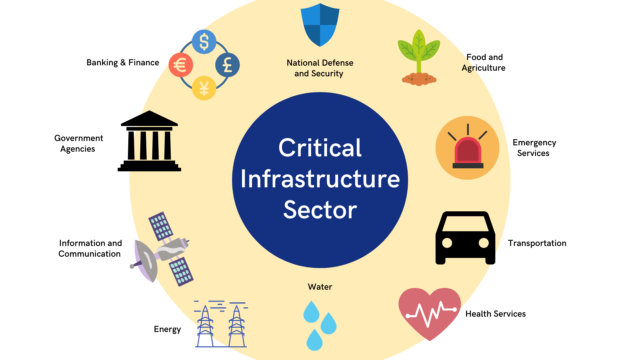
Telecoms sit at the intersection of all three. Modern states depend on global telecom networks for everything from:
Military command and control
Emergency services and critical infrastructure
Elections, banking and healthcare
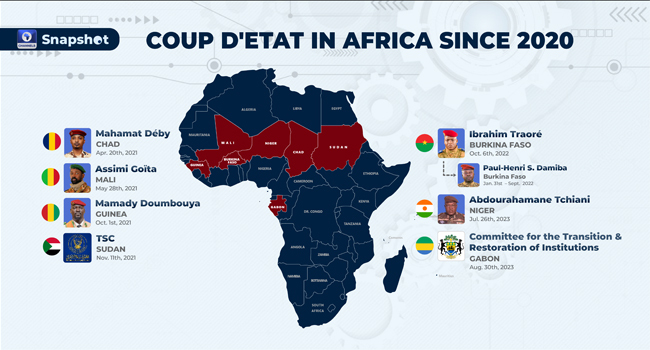
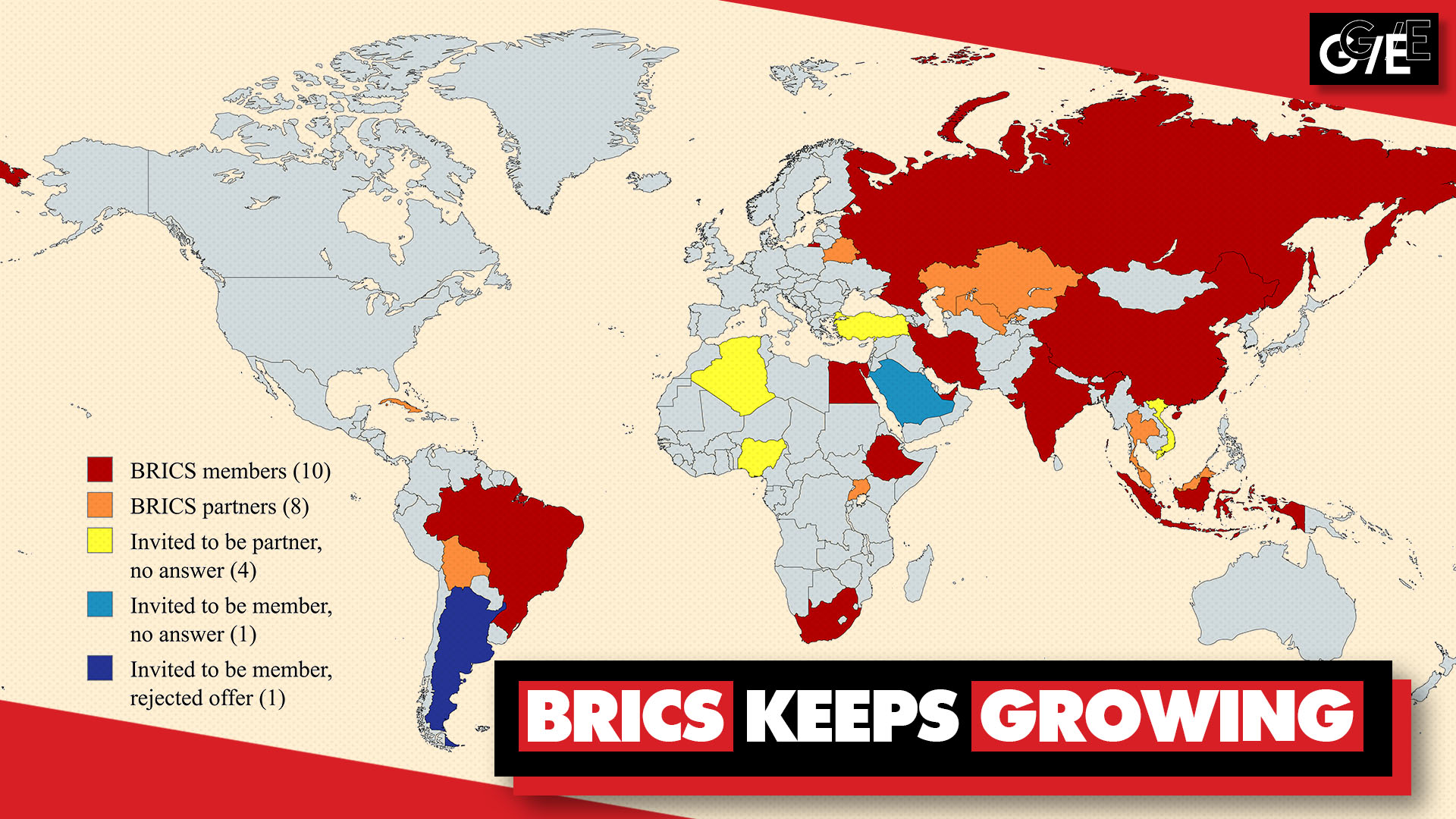
When those networks are compromised, physical security and digital security blur – a theme we’ve covered in The Rise of AI in Cyber Warfare and in discussions of hybrid conflict in African coups and global response.
Why signalling and “Global Titles” matter
Most users never think about signalling protocols like SS7 or Diameter, or about Global Titles – the special numbers mobile networks use to route signalling messages around the world.
But regulators have long warned that misconfigured or abused signalling allows attackers to:
Spoof caller IDs and SMS sender IDs
Intercept or reroute text messages, including one-time passwords
Track subscriber locations across networks
Inject traffic for spam campaigns and fraud
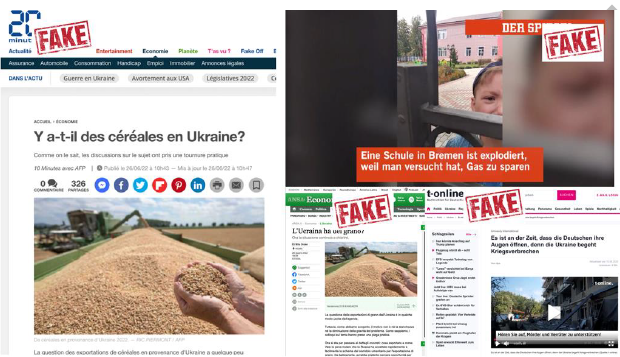
In parallel, AI tools now let criminals generate convincing messages and voices at scale, making telecoms not just a conduit, but an amplifier for fraud and influence operations – issues we also see in the context of disinformation campaigns targeted at democratic processes.
That’s the backdrop for November’s big regulatory move.
2. Five nations, one message: telecom regulators step up security
On 6 November 2025, telecom regulators and government agencies from the UK (Ofcom), US (FCC), Canada, Australia and New Zealand released a joint statement on telecommunications security cooperation, following meetings in London.
The statement commits to:
Enhanced cooperation on network reliability, integrity and security
Efforts to prevent exploitation and misuse of telecom resources such as Global Titles
Information sharing on emerging threats and fraud techniques, including SMS blasters and AI-driven fraud
Regular meetings to share best practices, mitigation strategies and regulatory developments
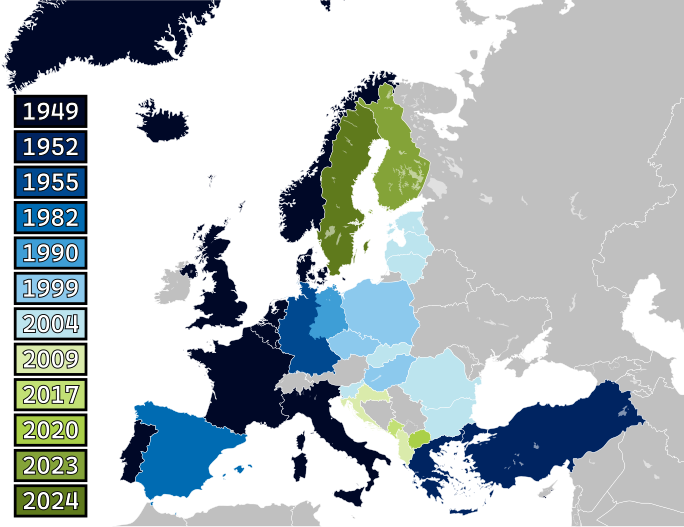
This is effectively a Five Eyes telecoms security club, complementing existing intelligence and cyber cooperation.
What this means for telecom operators
For operators, this isn’t just soft diplomacy – it foreshadows more concrete expectations and audits:
Stricter signalling security controls
Tight access control over Global Titles and signalling interconnects
Deployment of firewalls and anomaly detection across SS7/Diameter networks
Stronger vetting and monitoring of international roaming and A2P messaging partners
Anti-fraud obligations
Blocking known malicious SMS and voice traffic (including SMS blasting tools)
Better caller ID / sender ID validation to combat number spoofing
Cooperation with banks and government agencies to protect high-risk traffic like OTPs and alerts
AI risk management
Recognising AI both as a tool (for anomaly detection) and as a weapon (for scalable, personalised scams)
Participation in information-sharing schemes on AI-enabled fraud campaigns
Supply-chain scrutiny
More alignment with frameworks like the UK’s Telecoms Security Act, which gives government powers to designate “high-risk vendors” and impose controls on their equipment.
In practice, this will push telcos toward standardised baseline controls across the Five Eyes markets. For multi-national operators and vendors, that’s both a challenge and an opportunity: meet the bar in one country, and you’re much closer to compliance in the others.
What it means for equipment vendors and service providers
Vendors — from core network providers to SMS aggregators and signalling hubs — will feel the ripple effects in:
Procurement requirements – security certifications, signalling protections, AI and fraud-detection capabilities becoming deal-breakers rather than add-ons.
Contractual obligations – SLAs that include fraud metrics, incident reporting timelines and cooperation duties.
Regulatory visibility – greater likelihood of being named in guidance or enforcement action when systemic vulnerabilities are traced to specific products or services.
This increased scrutiny echoes broader patterns we’ve discussed in NATO’s Expansion and Arctic Militarization and in our piece on Australia’s new state-sponsor terrorism law: infrastructures and entities once seen as “commercial” are now treated as strategic assets or risks.
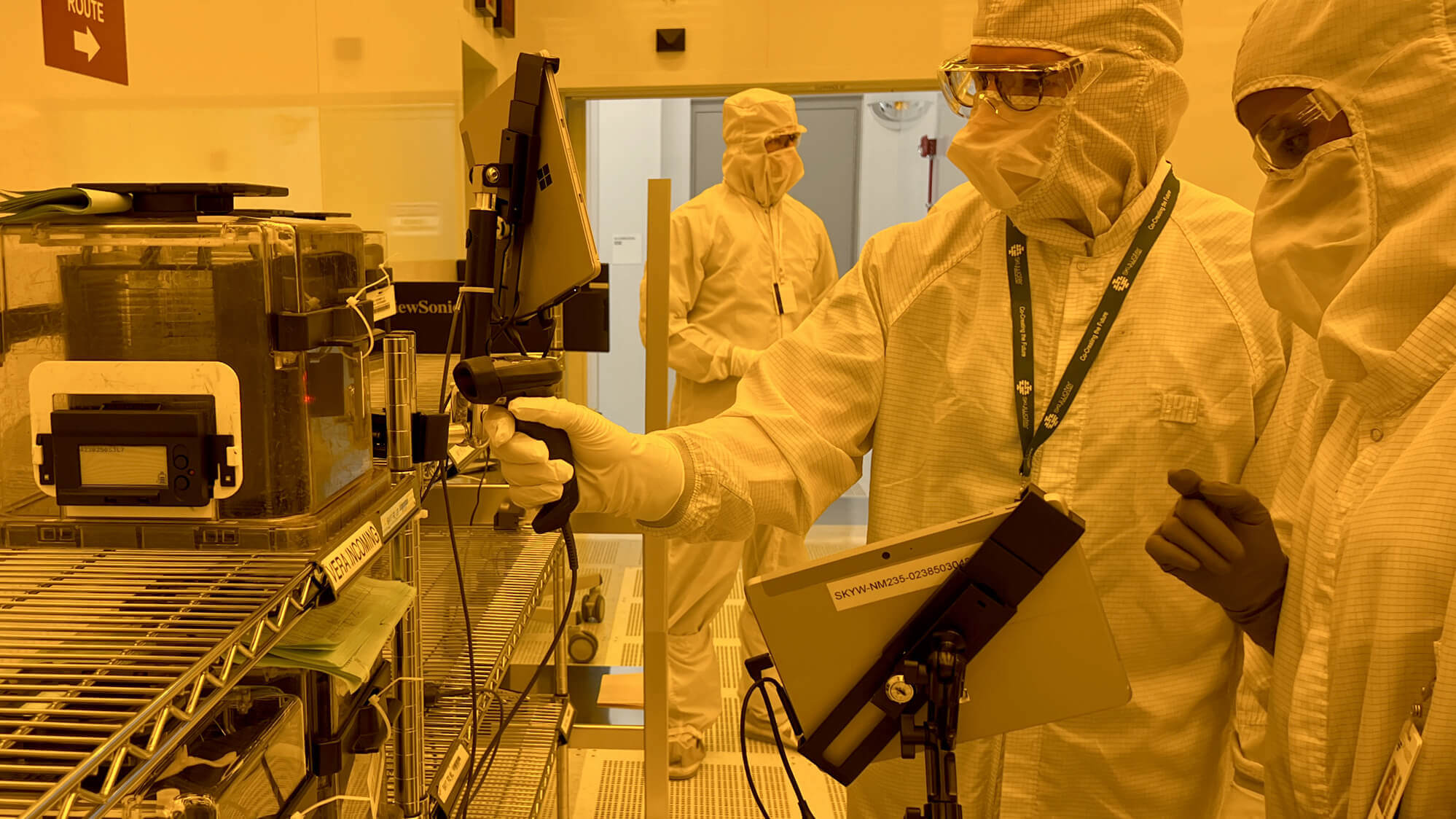
3. Device-level security: November’s Android bulletin and AV25-723
Regulators can harden networks, but the weakest link is often the device in your hand.
On 3 November 2025, Google published the Android Security Bulletin – November 2025, covering vulnerabilities fixed in the 2025-11-01 security patch level.
Security researchers and trade press quickly highlighted:
A critical remote code execution (RCE) vulnerability in the Android System component, exploitable over the network and in some scenarios without user interaction (a “zero-click” scenario).
At least one high-severity elevation of privilege issue, allowing attackers with a foothold on the device to escalate capabilities.
In parallel, the Canadian Centre for Cyber Security released advisory AV25-723, explicitly urging administrators and users to review the bulletin and apply updates. Other national CERTs, from Saudi Arabia’s NCA to EU member states, issued similar advisories pointing back to the same bulletin.
Why this month matters
There are three reasons November’s Android update is getting so much attention:
Zero-click risk
A critical RCE that can be triggered without user interaction is gold for attackers. It can be chained into powerful exploits for
spyware, banking malware or surveillance, particularly against high-value targets.
Wide version coverage
The bulletin and analyses indicate impact across multiple Android generations (commonly Android 13–16), meaning a very large installed
base is potentially vulnerable until patched.
Fragmented patching ecosystem
Not every device gets updates at the same time – or at all. Some OEMs roll out security patches slowly; others stop updating models
after a few years. Interestingly, the Pixel November 2025 bulletin shows no new Pixel-specific patches because recent Pixels already
contain the necessary fixes via earlier updates, underscoring how staggered and vendor-specific patch timelines can be.
What individuals should do (concrete steps)
If you’re an Android user:
Check your patch level
Go to Settings → About phone → Android version and look for the Android security update date.
Aim for 2025-11-01 or later; if your device is behind, check for updates now.
Enable automatic updates where possible
Leave OS and Google Play System updates set to auto.
Avoid delaying restarts for days or weeks when a security update is pending.
Reduce unnecessary risk
Avoid sideloading apps from untrusted sources.
Use Google Play Protect and consider a reputable mobile security app for business-critical devices.
Prefer app-based or hardware security keys over SMS for multi-factor authentication, reducing reliance on potentially vulnerable SMS channels.
What organisations need to do
For companies with fleets of Android devices (including BYOD):
Update your MDM policies to enforce a minimum security patch level, as close to 2025-11-01 as practical.
Segment high-risk users (executives, admins, finance) and prioritise patching for those devices.
Ensure your incident response plan includes playbooks for mobile compromise, not just servers and laptops.
Track OEM/device models that are out of support and plan device refreshes – don’t rely indefinitely on obsolete, unpatched hardware.
This device-level hygiene is the personal counterpart to the “big picture” cyber themes we explored in How Upcoming U.S. and EU Elections Are Influencing Global Security Strategies – where nation-state actors increasingly mix network intrusions, phishing and mobile exploits to pursue political ends.
4. Patch Tuesday in a shrinking OS landscape
Alongside the Android news, November also marks a turning point in the desktop OS world.
Windows 10: end of the road (for most)
Microsoft’s final free Patch Tuesday for Windows 10 landed on 14 October 2025, after which the OS has officially reached end of support. Users can keep running it, but they will no longer receive free security patches unless they enroll in a paid Extended Security Updates (ESU) programme.
Commentators and Microsoft itself estimate that hundreds of millions of devices still run Windows 10, many unable to upgrade to Windows 11 for hardware reasons.
November 2025 Patch Tuesday: fewer versions, same pressure
Security analysts note that the November 2025 Patch Tuesday environment is qualitatively different:
October saw a major push to clear vulnerabilities in products approaching end-of-life, including older Windows 10 releases, Windows 11 22H2 Enterprise/Education, and legacy Office and Exchange Server versions.
As those versions drop away, each new Patch Tuesday will cover fewer supported OS and app versions – but the systems left behind in the wild will gradually become softer targets, attractive to attackers who know they’ll never be patched.
For security teams, this means:
Tighter patch cycles for supported systems, especially for actively exploited vulnerabilities.
Strategic decisions about legacy systems: pay for ESU, isolate them aggressively, or retire and replace.
This is more than IT housekeeping. In an environment where states weaponise cyber vulnerabilities (as we discussed in AI in cyber warfare), unpatched legacy systems become national-scale liabilities.
5. Best practices for businesses and individuals
So what should organisations and ordinary users actually do in light of these November developments?
For businesses and public-sector organisations
Tighten your patch management game
Maintain an accurate asset inventory (including Android devices, servers, network equipment).
Classify systems by criticality and exposure (internet-facing, telecom-connected, privileged).
For high-severity or actively exploited vulnerabilities (like November’s Android RCE), adopt compressed patch timelines – days, not weeks.
Plan for the post-Windows 10 world
Decide whether to enrol in ESU for Windows 10, accelerate upgrades to Windows 11, or retire non-compliant devices.
Treat any unpatched legacy systems as if they’re permanently vulnerable: isolate them, restrict internet access, and monitor them closely.
Harden telecom interfaces and dependencies
If you operate your own telecom infrastructure or rely heavily on telecom APIs:
Audit your exposure to signalling networks, SMS aggregators and voice gateways.
Ask suppliers about their controls on Global Title abuse, SMS spoofing and fraud detection.
Implement controls to reduce dependency on SMS for critical security functions, shifting toward app-based or hardware authentication.
Strengthen monitoring and telemetry
Centralise logs from firewalls, endpoints, identity systems and telecom gateways into a SIEM or modern data platform.
Use behavioural analytics to detect anomalous device activity (e.g. Android devices suddenly contacting suspicious domains) or unusual telecom patterns (e.g. bursts of SMS traffic to high-risk destinations).
Refresh incident response and tabletop exercises
Incorporate telecom fraud, mobile compromise and supply-chain incidents into your scenarios, not just classic ransomware.
Align with national cyber-security guidance from bodies like the NCSC, Cyber Centre, CISA or your local equivalent.
For individuals
Keep everything up to date
Enable automatic updates for Android, iOS, Windows/macOS and key apps.
On Android, aim for security patch level 2025-11-01 or later.
Treat SMS and calls as untrusted
Be wary of unsolicited messages asking for payment, login or verification codes – even if they look like they come from a bank or government.
If in doubt, call back using an official number from a website or statement, not the number in the message.
Upgrade your authentication
Where possible, switch from SMS-based 2FA to app-based codes (e.g. Google Authenticator, Microsoft Authenticator) or hardware security keys.
Enable biometric locks and full-disk encryption on phones and laptops.
Reduce app and permission sprawl
Uninstall apps you no longer use.
Review app permissions (location, SMS, call logs, camera) and tighten where you can.
These aren’t glamorous steps, but they’re the digital equivalent of locking your doors and checking your smoke alarms.
6. What to watch next: AI, 5G/6G and beyond
November’s developments are snapshots in a much longer story. Over the next few years, expect the threat landscape to be shaped by several converging trends.
AI-powered telecom fraud and defence
Regulators and industry bodies are already warning that AI makes scams cheaper, faster and more convincing: deepfake voices, hyper-personalised SMS lures, and automated scam call centres.
At the same time, operators are investing in AI-driven systems to:
Detect anomalous signalling patterns and fraud campaigns
Spot synthetic voice signatures and bot-like call behaviour
Correlate telecom data with other signals of compromise
The regulatory cooperation announced this month will likely accelerate standard-setting around AI use in telecom security.
5G, 6G and edge computing
As 5G standalone, network slicing and edge computing roll out, the telecom network becomes even more software-defined and distributed. That brings:
New attack surfaces (APIs, slices, edge nodes)
New dependencies between telecoms and cloud providers
Harder questions about which country’s law applies where, especially for cross-border slices and IoT deployments
Looking ahead to 6G, debates about sovereign control, vendor trust and supply-chain security will intensify – echoing the high-risk vendor debates we’ve seen under the UK’s Telecoms Security Act and in EU 5G toolbox discussions.
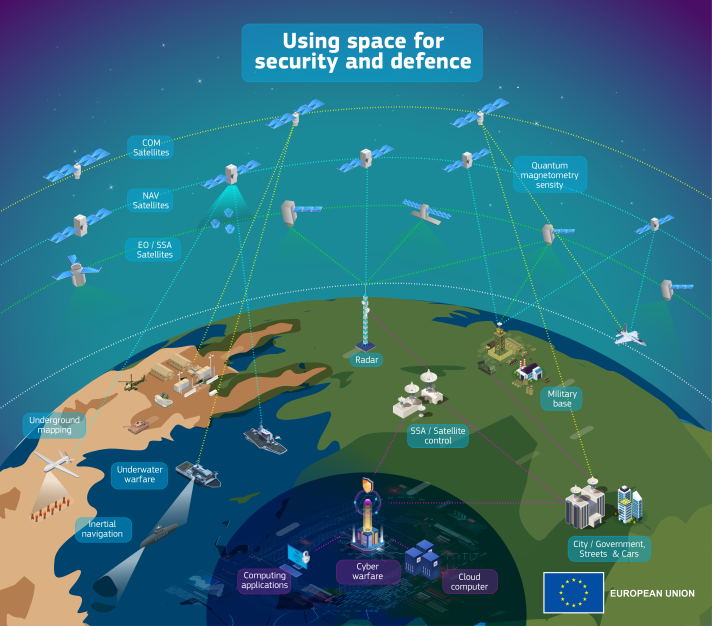
Satellites, quantum and beyond
We’re also entering an era where:
Satellite internet constellations become mainstream connectivity options, raising new questions about interception, jamming and jurisdiction.
Post-quantum cryptography slowly enters telecom and device standards, as states hedge against future decryption risks.
These topics may feel abstract now, but they mirror the trajectory we’ve seen in other domains: what begins as niche technical debate quickly becomes central to national security and regulation – just as AI did in the cyber-warfare space, and as we saw with state-backed terrorism designations in Australia.
Security in the layers you don’t see
November 2025 has underlined a simple truth:
The systems that feel invisible – signalling networks, firmware updates, cloud APIs – are now some of the most important terrain in modern security.
Telecom regulators across the Five Eyes are coordinating to harden networks against signalling abuse, SMS blasting and AI-driven fraud. Android’s November bulletin and advisory AV25-723 underscore how a single zero-click vulnerability can put millions of devices at risk. And the end of free updates for Windows 10 forces organisations to reckon with a future where unsupported OSes quietly become attack magnets.
For governments, this is about national resilience and deterrence. For businesses, it’s about matching regulatory expectations with real technical controls. For individuals, it’s about taking device security and digital hygiene seriously – because in a hyperconnected world, your phone and laptop are part of the frontline too.
Across our series – from AI in cyber warfare to the EU’s Centre for Democratic Resilience and Australia’s state-sponsor terror law – one pattern keeps emerging:
Security is no longer just about borders and battlefields. It’s about networks, devices and data, and the often unseen choices we make in how we build, regulate and use them.
Those who understand and secure these unseen layers today will be the ones best positioned to weather the threats of tomorrow.