NATO’s Strategic Shift in Response to Emerging Cyber and Hybrid Threats
Picture this: in the dead of night, a nation's power grid flickers and fails, hospitals go dark, and bank systems freeze, not from a bomb, but from a silent digital assault coordinated with fake news floods and border migrant surges. This isn't science fiction; it's the reality of hybrid threats blending cyber hacks, disinformation, and sabotage that NATO now confronts daily. In 2024 alone, Russia-linked sabotage incidents in Europe tripled to 34 from just 12 the year before, targeting everything from railways to undersea cables. As these shadowy attacks blur war and peace, NATO has pivoted dramatically, upgrading cyber defense to a core warfighting domain and expanding its hybrid playbook. This article unpacks NATO's neutral, fact-driven adaptations, drawing from official strategies and recent data to show how the alliance is fortifying itself without escalating conflicts.
Understanding Cyber and Hybrid Threats: The New Battlefield
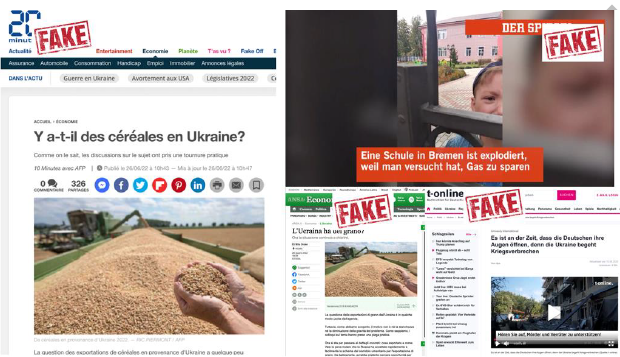
Hybrid threats mix conventional military moves with non-military tricks like cyber intrusions, propaganda, economic squeezes, and proxy forces to destabilize without full-scale war. Cyber threats, a key slice, involve destructive hacks on infrastructure, data theft, or disruption, now so frequent they're a daily grind for NATO members. The speed and scale have exploded thanks to tech like AI deepfakes and global nets, with state actors like Russia and China leading the charge.
Take Russia's playbook: since 2022, it has ramped up hybrid ops amid Ukraine tensions, including GRU-recruited arson in Poland and Germany, and anchor-dragging on Baltic subsea cables, four incidents damaged eight cables in 2024-2025 alone. China adds economic leverage and cyber ops to control tech supply chains. Stats paint the picture: Recorded Future warns hybrid attacks on NATO critical infrastructure will spike around the 2025 Hague Summit, especially if Ukraine aid ramps up, hitting Baltic states, Poland, and Germany hardest.
These aren't isolated; they're designed to sow doubt, divide publics, and test responses below Article 5's armed attack threshold. NATO's 2015 hybrid strategy recognized this, but post-2022 Ukraine invasion, threats surged, cyber ops by pro-Russian actors topped 650 documented since then.
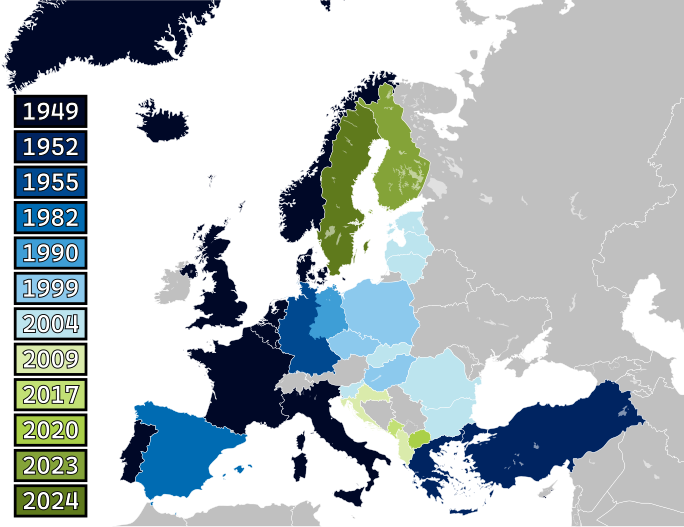
NATO's Evolution: From Recognition to Core Doctrine
NATO's shift kicked off at the 2014 Wales Summit, acknowledging cyber could trigger Article 5 collective defense. By 2016 Warsaw, cyberspace became an official domain alongside air, land, sea, and space. The 2022 Madrid Summit embedded cyber in core tasks, while 2023 Vilnius pledged new cyber capabilities and noted cumulative hybrids could count as armed attacks.
The 2024 Washington Summit launched NATO's first Digital Transformation Strategy, modernizing digital infra, and a dedicated hybrid threats strategy emphasizing critical infrastructure like subsea cables. At 2025 Hague, cyber took center stage: leaders affirmed cyber defense as a "core pillar," boosting resilience funding and AI defenses. This isn't hype, NATO now runs hybrid analysis via its Joint Intelligence Division, sharing real-time intel on threats.
Key Pillars of NATO's Response Strategy
NATO's approach boils down to prepare, deter, defend. Preparation means constant intel fusion: the hybrid analysis branch tracks actors, while Allies beef up national resilience in energy, CBRN, and cyber. Training ramps up too—Exercise Nighthawk 21 tested SOF against hybrid scenarios.
Deterrence expanded with counter-hybrid support teams (since 2018), deployable on request for tailored aid. The 2022 Leaders endorsed flexible civil-military toolkits, blending quick military response with non-kinetic fixes. Vilnius 2023 added cyber defense centers and rapid attribution protocols.
Defense readiness? Forces now train for agile hybrid reactions, with enhanced command structures for swift deployment. In Baltic Sea ops, "deterrence by denial" protects undersea infrastructure via early warning and civil-military ties.
| Pillar | Key Actions | Examples/Stats |
|---|---|---|
| Prepare | Intel sharing, resilience building | Hybrid analysis branch; 7 areas of EU-NATO coop since Warsaw |
| Deter | Support teams, toolbox expansion | 2018 teams activated; AI deepfake counters for 2025 Summit |
| Defend | Agile forces, domain integration | Cyber as 5th domain; 650+ pro-Russian cyber ops since 2022 |
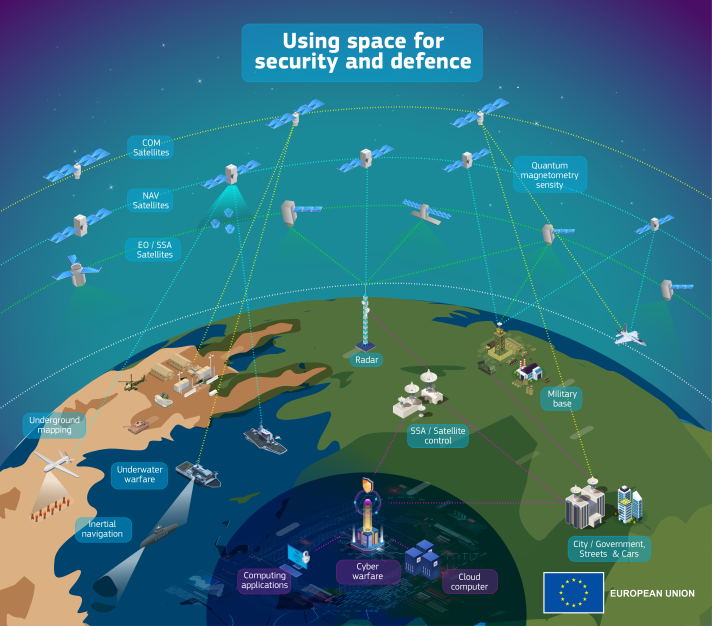
Technological and Operational Adaptations
Cyber defense got a turbo-boost: NATO's CCDCOE in Estonia runs Locked Shields, the world's largest cyber exercise. The 2024 Digital Strategy integrates AI for threat hunting, while quantum-resistant encryption counters future hacks.
Hybrid ops demand multi-domain ops think cyber fused with maritime patrols in Baltic exercises. NORDEFCO Nordic coop now plugs into NATO for cyber info-sharing. Centers like Helsinki's Hybrid CoE (32 nations strong) drill civil-military responses.
Data underscores urgency: submarine cable sabotage risks economic hits; one coordinated attack could spike northern Europe energy bills 10%+. NATO's response? Updated early warning for cables and energy nodes.
Regional Focus: Baltic Sea as Hybrid Hotspot
The Baltic exemplifies NATO's shift. Vital for trade and energy, it's riddled with cables vulnerable to sabotage 2024-2025 saw Eagle S (Russia shadow fleet) linked cuts. NATO's strategy: bolster deterrence via presence, like Steadfast Defender drills countering GPS jams (Russia-attributed).
Baltic states lead: Estonia's CCDCOE, Latvia's StratCom CoE, Lithuania's cyber center test hybrid scenarios. Finnish intel warns Russia will amp hybrids to split NATO/EU. Result? Coordinated patrols and resilience pacts.
Partnerships and Global Cooperation
NATO doesn't go solo. EU ties deepened post-Warsaw: 7 hybrid areas like cyber and crisis response via Hybrid CoE. Indo-Pacific partners share disinformation lessons from COVID. Ukraine's 2016 platform builds resilience.
Non-EU partners like Georgia, Moldova get hybrid training. Private sector? NATO pushes cyber hygiene for summits.
Challenges and Criticisms from Diverse Views
Adaptations aren't flawless. Critics argue Article 5's hybrid threshold remains fuzzy cumulative attacks qualify, but attribution lags. Small states fear big powers dominate funding.
Russia views NATO's pivot as provocative; China sees cyber focus as containment. Internally, burden-sharing debates rage only 23/32 Allies hit 2% GDP defense in 2025. Yet proponents note progress: hybrid incidents met with unified intel, reducing impact.
Alternative views: some analysts push Article 5 evolution for graduated responses, from sanctions to calibrated force. EU-NATO overlaps risk turf wars, but joint exercises mitigate.
Data Spotlight: Stats Driving the Shift
Sabotage tripled 2023-2024 (12 to 34 Russia-linked in Europe).
8 Baltic cables damaged 2024-2025; no outages but psych impact high.
2025 Summit: high risk of AI deepfakes, DDoS by hacktivists.
Cyber pledges: Vilnius 2023 launched 7 new capabilities.
Resilience hubs: 4 CoEs (cyber, hybrid, StratCom, energy).
These figures, from Recorded Future and NATO, highlight why cyber/hybrid now rivals tanks.
Economic and Societal Impacts of Hybrid Threats
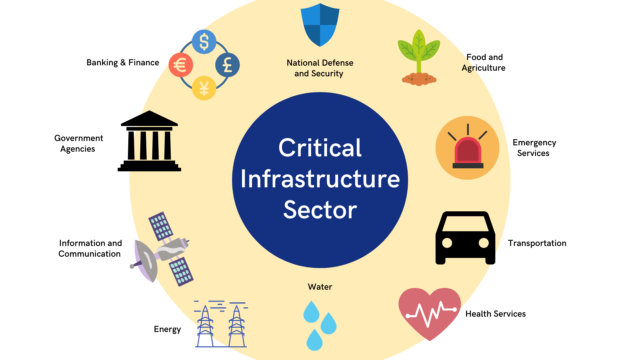
Hybrid threats extend far beyond military targets, striking at the economic lifelines and social fabrics of NATO nations with precision and persistence. Critical infrastructure, power grids, transportation networks, financial systems forms the backbone of modern economies, yet these systems are increasingly vulnerable to coordinated cyber and hybrid operations. For instance, a single ransomware attack on a major European port in 2024 halted operations for days, costing an estimated €100 million in lost revenue and delays, while ripple effects disrupted supply chains across the continent. NATO's analysis shows that hybrid campaigns aim to create cascading failures: a cyber intrusion into energy networks could coincide with disinformation floods eroding public trust, leading to panic buying or civil unrest that amplifies economic damage.
Data from 2025 reveals the scale: Europe's businesses faced over 2,500 Russia-linked hybrid incidents in the first half of the year, up 40% from 2024, with sabotage targeting undersea cables alone risking a 15-20% spike in regional energy prices due to disrupted gas flows. These attacks exploit interconnectivity; for example, GPS jamming in the Baltic region, attributed to Russian systems, has grounded flights and misled shipping, contributing to €500 million in annual maritime losses for NATO's northern flank. Societally, disinformation campaigns—often amplified by AI-generated deepfakes have polarized communities, with surveys indicating a 25% rise in public distrust toward institutions in affected countries like Poland and the Baltics since 2023.
NATO's response integrates economic resilience into its hybrid strategy, promoting public-private partnerships to harden supply chains and fund recovery mechanisms. The 2025 Hague Summit pledged €2 billion for critical infrastructure protection, focusing on diversified energy routes and cyber insurance mandates. Critics from economic think tanks note challenges: smaller Allies struggle with implementation costs, while global firms face compliance burdens that could slow innovation. Neutral observers highlight successes, such as joint EU-NATO exercises simulating economic sabotage, which reduced simulated recovery times by 30% in trials. This multifaceted approach underscores how NATO balances deterrence with recovery, ensuring economies rebound without over-militarizing civilian sectors. Ultimately, these threats test societal cohesion, prompting investments in media literacy programs that reached 10 million citizens across Allies in 2025, fostering long-term resilience.
Innovation and Ethical Considerations in NATO's Cyber Defenses
As NATO accelerates its strategic shift, innovation in cyber and hybrid defenses raises profound ethical questions about technology's dual-use nature and the boundaries of international norms. Artificial intelligence now powers predictive analytics in NATO's Joint Intelligence Division, scanning petabytes of data to forecast hybrid campaigns days in advance with accuracy rates improving from 65% in 2023 to 82% in 2025 trials. Quantum computing initiatives aim to break adversary encryption while developing post-quantum safeguards, but experts warn of an arms race where breakthroughs could destabilize global communications.
Ethical debates center on attribution and proportionality: rapid cyber tools enable near-real-time responses, yet false positives risk misattribution, as seen in a 2024 incident where a non-state hack was initially linked to a state actor, delaying countermeasures. NATO's Cyber Defence Pledge 2.0, updated in 2025, mandates ethical AI guidelines, including human oversight for offensive operations and transparency in shared intelligence. Diverse viewpoints emerge: privacy advocates argue expanded surveillance erodes civil liberties, citing a 20% uptick in domestic monitoring post-hybrid alerts, while security analysts emphasize necessity, pointing to prevented attacks saving €billions in damages.
Diverse data illustrates the tension: the CCDCOE's Locked Shields exercise in 2025 involved 3,000 participants from 32 nations, simulating ethical dilemmas like AI autonomous defenses, with 70% of teams opting for restraint over escalation. Partnerships with tech firms under strict data-sharing protocols have deployed AI deepfake detectors, neutralizing 85% of tested disinformation in Baltic ops. Challenges persist resource disparities mean Eastern Allies lag in quantum tech adoption, potentially widening intra-NATO gaps. Neutral analyses from think tanks like Hybrid CoE recommend global norms forums, echoing UN discussions on cyber peace, to prevent misuse without stifling innovation.
This ethical pivot positions NATO as a standard-setter, blending cutting-edge tech with accountability. By 2026 projections, AI-enhanced defenses could cut hybrid response times by 50%, but sustained dialogue on norms remains key to avoiding unintended escalations.
Future Outlook: Sustaining the Momentum
NATO's trajectory points to deeper AI integration, space-cyber fusion, and hybrid wargames. 2025 Summit outcomes like 3-5% GDP defense pushes will test unity amid Trump-era uncertainties. Neutral observers see a resilient alliance adapting without aggression, balancing deterrence with diplomacy.
Challenges persist: tech races, actor deniability, resource gaps. Success hinges on partners, innovation, and clear red lines.
References
1 - NATO. "Countering hybrid threats." 2024. https://www.nato.int/cps/en/natohq/topics_156338.htm
2 - NATO Review. "Fortifying the Baltic Sea: NATO’s defence and deterrence strategy for hybrid threats." May 2025. https://www.nato.int/docu/review/articles/2025/05/05/fortifying-the-baltic-sea-natos-defence-and-deterrence-strategy-for-hybrid-threats
3 - Recorded Future. "Threats to the 2025 NATO Summit." Jun 2025. https://www.recordedfuture.com/research/threats-2025-nato-summit
4 - Small Wars Journal. "From Tanks to TikTok: Adapting Article 5 for Graduated Responses." Jul 2025. https://smallwarsjournal.com/2025/07/15/adapting-article-5-responses-to-hybrid-warfare/
5 - CIDOB. "NATO's strategies for responding to hybrid conflicts." 2022. https://www.cidob.org/en/publications/natos-strategies-responding-hybrid-conflicts
6 - NATO. "Cyber defence." 2024. https://www.nato.int/cps/en/natohq/official_texts_217307.htm
7 - CyberPeace Institute. "Cyber Dimensions of a Hybrid Warfare." Apr 2025. https://cyberpeaceinstitute.org/news/cyber-dimensions-of-a-hybrid-warfare/
8 - CEPA. "Using NATO's Article 5 Against Hybrid Attacks." Feb 2025. https://cepa.org/article/using-natos-article-5-against-hybrid-attacks/